Would da Vinci Support the Pentagon’s New Cyber Strategy?
Jessica ‘Zhanna’ Malekos Smith
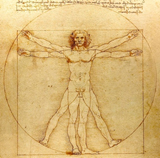
Leonardo da Vinci’s notebook on Art and Life holds many fascinating observations on painting, human nature, and warfare. But based on these insights, how might da Vinci advise the Defense Department about its new strategy for cyberspace operations?
First, the Cyber Strategy Summary describes defend forward as “confronting threats before they reach U.S. networks” with two core elements: the strategic persistent engagement of adversaries and working with allies and partners to promote security.
Da Vinci would probably call this military strategy a misnomer.
Using a hunting example, he invites us to imagine how inefficient an archer’s reach would be if they constantly held a forward-leaning posture. Noting that if “anyone wishes to make a bow carry a very long way, he should draw himself up on one foot, raising the other so far from it as to create the necessary balance for his body, which is thrown forward on the first foot and he should not leave his arm fully extended.” Archery tips aside, the sharpest contemporary critiques of defend forward are that it is “a vague concept” and “promises to do too much all the time and doesn’t articulate priorities[.]”
Instead, a concept that more accurately conveys U.S. Cyber Command’s strategy and is derived from this Italian polymath’s writings is defense impetus.
Defense Impetus?
Impetus is a type of power that a mover impresses upon a moveable thing.
Da Vinci explains “[e]very impression tends to permanence or desires permanence;” such as the impression of sound when the clapper strikes the bell, or the visual impression made by the sun’s glare on one’s eyes. Similarly here, defense impetus is a power impressed by CYBERCOM’s 133 cyber mission force teams upon the moveable target, or adversary.
To understand impetus in theory and in practice, let’s examine some of CYBERCOM’s recent known cyberspace operations:
In 2018 CYBERCOM exercised defense impetus by conducting an operation to disrupt the Internet access of the Russian troll factory (the Internet Research Agency), on the day of the midterm election. The operation’s objective, or desired impression, was to deter foreign interference in the U.S.’ elections. In 2019 CYBERCOM exercised defense impetus by disabling a critical database used by Iran’s paramilitary forces. Here, the desired impression was to curtail Iranian aggression after Iran launched a surface-to-air missile on an unmanned U.S. Navy MQ-4 surveillance aircraft and waged mine attacks against tankers in the Strait of Hormuz.
Focusing on deterrence, the congressionally established Cyberspace Solarium Commission is exploring “looking at a strategy built around deterrence through punishment” and will publish its formal report in several months. Defense impetus can help the Commission develop its strategy by exploring patterns of how the impression of each cyber operation, whether it’s by a state or non-state actor, tends to permanence, or desires permanence.
Another facet of defense impetus is collaboration. One example is CYBERCOM’s ongoing information sharing and training efforts with Montenegro, a NATO ally, to promote election security in 2020. According to CYBERCOM’s executive director, David Luber, the agency is “seeing some very interesting malware and other activities when we conduct some of those defend-forward missions . . . . Then we take that information and we share that broadly with industry and the rest of the government.” Collectively, CYBERCOM’s operations —impressions — are designed to protect the U.S. and its allies, and signal strength and deterrence to competitors. Defense impetus therefore best embodies the Pentagon’s objectives to compete and deter aggressive actions in cyberspace, and General Paul M. Nakasone’s vision of strategic persistent engagement and collaboration.
According to Brandon Valeriano, a senior advisor to the Solarium Commission, a major shortcoming of “defend forward” is that it unfortunately lacks a “"clear conception of metrics" to measure the success of the new strategy.”
So, What Should the Metrics Be?
Drawing inspiration from da Vinci’s observations on force, power, and movement – elements in which “all the works of mortals have their beginning and their end” – this article suggests four cyberspace operations principles. The following principles are intended to augment CYBERCOM’s strategy as it flexes its new authorities to take action outside Defense Department information networks. Below, resources refers to money, human capital, and materials, and force refers to the operational scope, or offensive parameters of cyberspace operations.
Defense Impetus Principles
- Principle 1: If you double the resources and not the force in the cyberspace operation, it becomes necessary to double the time to execute it.
- Principle 2: If you double the resources and not the force, nor the time to execute, it becomes necessary to halve the mission objectives of the cyberspace operation.
- Principle 3: If you double the resources and not the mission objectives of the cyberspace operation, nor the time to execute, it becomes necessary to double the force.
- Principle 4: If you halve the resources and not the mission objectives of the cyberspace operation, nor the time to execute, then the force is halved.
This concept can serve as a useful starting point to help CYBERCOM measure the progress of its strategy — but only if it’s willing to consider new paradigms. For as da Vinci encourages us, “it is by testing that we discern fine gold.”
About the Author(s)
Comments
We are committed to…
We are committed to providing our clients with exceptional solutions while offering web design and development services, graphic design services, organic SEO services, social media services, digital marketing services, server management services and Graphic Design Company in USA.
Thanks to you, a very…
Thanks to you, a very informative cybersecurity article. I am collecting materials to prepare an essay on cybersecurity for children and cyberbullying. Now I want to use data and from here in my work. Check out similar studies here https://writingbros.com/essay-examples/cyber-bullying/ but this isn't about strategy, it's about cyberbullying. But they also compare theses for clearer narration and foresight of the example. In general, I believe that the strategy should be justified not only strategically, but also financially. And, of course, it's clear how important strategy is, but pay attention to how time and money will be spent. Read also another point of view here https://www.cisco.com/c/en/us/products/security/cybersecurity-strategies.html There are other areas in our country that require such attention.
